Dark Web Monitoring for
Australian Businesses
Protect Your Business from Threats, Downtime, and Compliance Risks
Find out fast when your company’s credentials and data appear for sale
and act before criminals do.
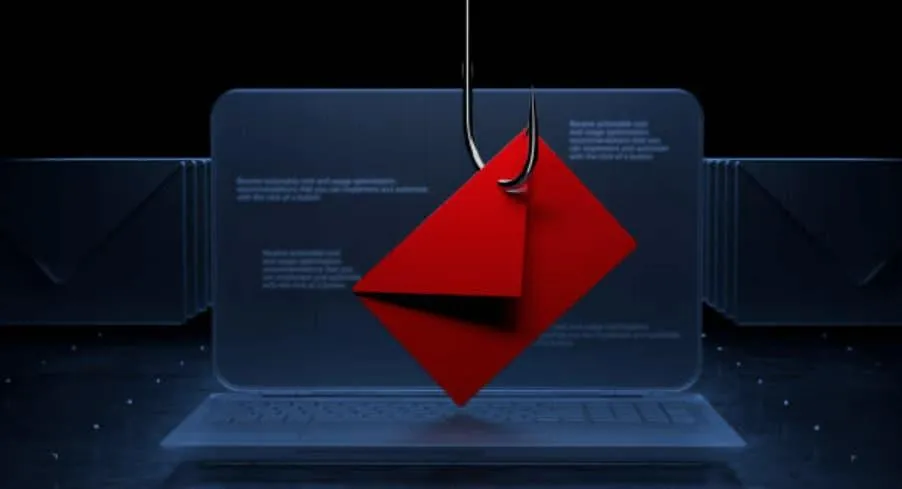
Your team uses dozens of apps and logins every day. When even one password is stolen in a phishing attack or a vendor breach, it can end up traded on criminal marketplaces across the dark web — putting your email, files, and customer data at risk. Tech Guard’s Dark Web Monitoring gives you continuous visibility into those hidden places, with rapid alerts and guided remediation so small and mid-sized businesses can stay a step ahead.

What is the dark web — and why should you care?
The dark web is a part of the internet that isn’t indexed by search engines and requires special tools to access. It’s where cybercriminals advertise and trade stolen credentials, corporate email/password pairs, session cookies, credit card numbers, and full data dumps from breached services. Most victims never know their details are circulating until an attacker logs in.
For businesses, the risks include:
Account takeover (ATO): attackers log into Microsoft 365, Google Workspace, Xero, or other apps using valid credentials.
Business email compromise (BEC): fraudulent invoices, payroll changes, and wire transfers that look like they came from you.
Ransomware & data theft: credentials are a common first step to planting malware and exfiltrating sensitive files.
Compliance exposure: loss of personal information can trigger reporting requirements and penalties under the Privacy Act and industry frameworks.
How Dark Web Monitoring works
Our platform continuously collects and correlates data from breach forums, dump sites, paste services, invite‑only marketplaces, and private threat‑intel feeds.
We monitor for:
Company domains (e.g., @yourcompany.com)
Executive and high‑risk accounts
Employee credentials exposed in third‑party breaches
Leaked API keys, tokens, and secrets
Mentions of your brand, projects, or internal tools
When a match appears, our system validates it, scores the severity, and notifies your nominated contacts. You get a clear plan to contain the risk and prevent misuse.
What you get with Tech Guard
Always‑on monitoring
24/7 scanning for your domains, VIPs, and key assets
High‑fidelity detections with human analyst review to cut noise
Actionable alerts
Context: breach source, exposure time, and which users/assets are affected
Priority scoring so your team knows what to do first
Rapid remediation
Guided steps for password resets, MFA enforcement, session revocation, and access reviews
Optional hands‑on help from our security engineers if you’d like us to do it for you
Executive‑ready reporting
Monthly exposure summaries and trendlines
Evidence packs for auditors, cyber insurance, and board updates
Awareness & prevention
Targeted security training for affected users
Policy recommendations to reduce future exposure (password managers, SSO, conditional access, and more)
The remediation playbook (what happens when we find something)
Alert issued — you receive an email/SMS/portal alert with severity, affected accounts, and recommended actions.
Contain — force password resets, revoke active sessions, rotate keys, and enable/verify MFA.
Harden — review access rights, create conditional access policies, and update phishing protections.
Educate — quick coaching for the impacted user so the same mistake doesn’t happen twice.
Report — an incident summary with evidence and lessons learned, suitable for compliance and insurance.
Most incidents can be contained within minutes when detected early.
Our Managed Cyber Security Services

Incident Response
Round-the-clock monitoring detects and neutralises potential threats in real time. Our incident response team ensures swift action to mitigate risks and prevent further damage.
Foster an office atmosphere that energizes your team

Advanced endpoint detection and response (XDR) tools safeguard your devices against malware, ransomware, and unauthorised access.

We continuously scan the dark web for compromised credentials or sensitive data, alerting you before issues escalate.
Email Security
Our robust email security solutions, including phishing simulations and smart filtering, protect your team from fraudulent emails and attacks.

Disaster Recovery
Prepare for the unexpected with secure backups and disaster recovery solutions that ensure fast data restoration and minimal downtime.

Empower your team with practical training to identify threats, avoid phishing scams, and practice safe online behaviour.
Why businesses choose us
Built for SMBs: enterprise‑grade monitoring without enterprise complexity.
Local support: Australian team that understands local compliance expectations and business hours.
End‑to‑end help: from detection to remediation to prevention — one partner, clear accountability.
Plays nicely with your stack: Microsoft 365, Google Workspace, Azure AD/Entra ID, Okta, popular CRMs and accounting suites.


Who benefits from Dark Web Monitoring?
Professional services (legal, accounting, financial advisers) handling confidential client data
Healthcare & community services with sensitive personal information
Construction, manufacturing, and trade businesses with project IP and supply‑chain access
Retail & eCommerce where staff share access to sales and payment platforms
Any business using cloud apps and remote work — which is most businesses today
Is this legal?
Yes. We monitor publicly available breach data, underground marketplaces, and threat‑intel sources without participating in criminal activity. We do not hack, buy stolen data, or access systems without permission.
Does this stop breaches from happening?
Monitoring doesn’t prevent a third‑party site from being hacked, but it does limit the damage by telling you quickly when your credentials are exposed so you can reset passwords, enforce MFA, and block suspicious logins.
We already have MFA. Do we still need this?
Absolutely. MFA dramatically reduces risk, but attackers still attempt MFA fatigue attacks, token theft, and social engineering. Monitoring adds an early‑warning layer and helps you find weak or reused passwords before they’re abused.
Will this create lots of noisy alerts?
No. We focus on high‑confidence matches for your domains and accounts, and our team reviews ambiguous finds. You’ll only see alerts that matter, with clear next steps.
Can you monitor personal emails for executives?
Yes — with consent. Many breaches start with a personal account that’s reused for work. We can include selected non‑work emails and phone numbers for added protection.
How quickly will we be notified?
As soon as a verified exposure is detected. Alerts are near‑real‑time for many sources; some private dumps are batch‑released, in which case you’ll be notified right after ingestion and validation.
Is there a report we can give to the board or our insurer?
Yes. You’ll receive monthly summaries and on‑demand incident reports showing what was found, how we responded, and how risk is trending over time.
Innovation
Fresh, creative solutions.
Integrity
Honesty and transparency.
Excellence
Top-notch services.
Legal Firms
Engineering
Real Estate
Medical / Dental
Contruction
Copyright 2026. Tech Guard IT Services Pty Ltd. All Rights Reserved. / Site Map / Legal / Policy / ABN: 67 672 354 353
